My Mom Started Messaging Me… Two Weeks After Her Death: Families Traumatized by New ‘Ghost Hacking’ Scam Targeting Dead People
It was two weeks after her mother’s death and Melanie’s grief was just beginning to subside when a notification appeared on a younger relative’s phone.
Much to the family’s shock, it was a Facebook DM from her late mother. ‘Hello how are you today?’ read the message.
Reading it caused a flood of emotions in Melanie; for a split second there was a glimmer of hope that she might still be alive.
Then came the sudden realization that something sinister was going on.
Melanie – who wished to remain anonymous to avoid the family being targeted again – fell victim to an emerging new scam, ‘ghost hacking’.
The scammer quickly turned to selling fake investment opportunities (Photo: Daily Mail)

Melanie says the hacker struck within two weeks of her mother’s death
Ghost hacking involves hackers targeting the accounts of recently deceased people, either for outright theft or to message family members with scams.
Melanie says her mother, who died after a short illness, started messaging family members from a cloned Facebook account.
Melanie believes hackers may have looked at obituaries or local news reports about recent deaths to find victims to target.
She told DailyMail.com: ‘It was quite upsetting, not just for me but for my whole family because mum was such a character within the family. ‘
In Melanie’s case, the hacker contacted a young relative at university and said that Melanie’s mother had recently found a brilliant investment opportunity.
Melanie said: ‘The conversation started with a simple: ‘Hello, how are you?’ and then the hacker proceeded to run a $150,000 compensation payment scam.
Melanie said the hacker appeared to be using a cloned Facebook account and it was “incredibly difficult” to contact Facebook to stop this.
The family had not considered dealing with her mother’s online accounts due to the rapid events surrounding her mother’s death.
“I want to prevent other people from having to go through what we did,” Mel said.
‘You need to think about the person’s digital presence while he or she is still alive – and your own in case the worst happens.’
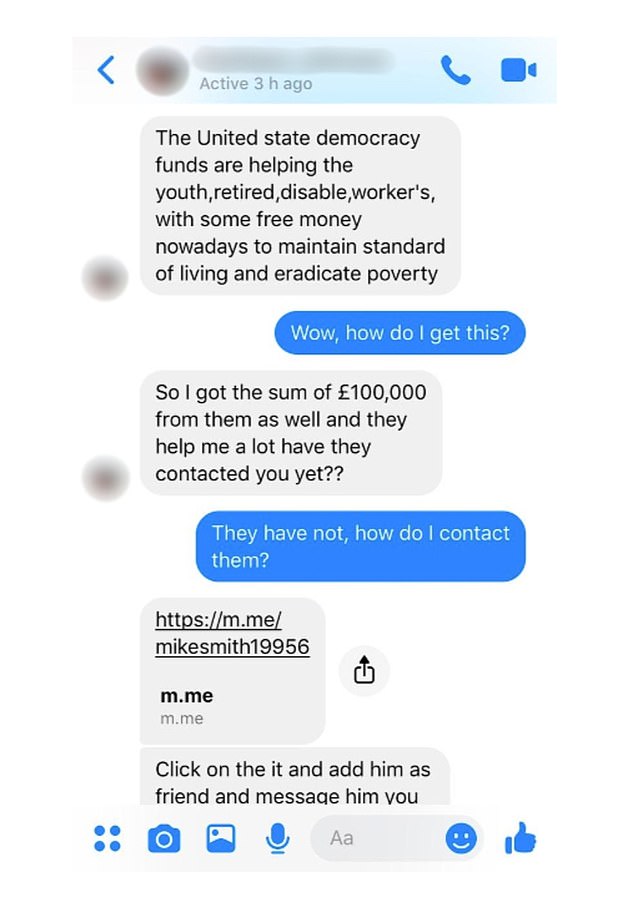
The scammer quickly tried to trick Mel’s cousin into visiting a fake web page (Picture Daily Mail)
Hackers use obituaries to identify people who have recently died and attempt to hack into email and social media accounts.
Hackers then often try to empty bank accounts and pension funds, or take out loans in the name of the deceased.
Sometimes the hackers use the person’s email and social accounts to send spam and scams to family members.
It’s easier to take control of dead people’s accounts because no one is monitoring the activity, and once in the email, hackers can move on to more valuable financial accounts, for example.

Hackers target recently deceased people to steal from their accounts
Patrick Tiquet, VP of security and compliance at Keeper Security, said: “Cybercriminals can use obituaries, social media profiles and public records to track down the deceased and the potentially vulnerable accounts they left behind.
“Bad actors can then use advanced techniques to launch cyberattacks to breach these ‘ghost’ accounts, abusing weak passwords, asking forgotten security questions, or even using stolen credentials obtained from previous data breaches.
Hackers can ‘merge’ data from previous leaks, or data shared online, to gain access to ‘ghost accounts’, Tiquet warns.
Tiquet said: ‘Cybercriminals wait for their opportunity to strike and target individuals of all ages, backgrounds and walks of life – both in life and after people have died.
“Data breaches happen every day that could compromise personally identifiable information (PII) and this trove of data finds its way to the dark web, where it is eagerly bought and sold. Cybercriminals can use this stolen information to commit even more crimes, such as identity theft or financial fraud, leaving families in disarray as their loved one’s estate is tarnished by unseen hands.
The key to avoiding falling into the clutches of ‘ghost hackers’ is to think ahead and set options to ‘remember’ accounts – or ensure a family member is present to memorialize or delete accounts.
Facebook and Google, for example, offer the option to create a legacy contact who can take over the account after death.
Click here to visit Google’s ‘inactive account manager’ and set up a contact to ‘take over’.
To create a ‘legacy contact’ on Facebook who will take over your account in the event of your death, click here.
Tiquet says: ‘Take a digital inventory of your online presence, assets and liabilities; appointing a digital heir to receive your login details and assets; and coming up with a plan, such as storing login credentials and personal documentation in a secure password manager that can be passed on to your digital heir, will ensure your digital presence can rest in peace.
“Protecting our digital legacies isn’t just about protecting our online efforts today; it is also about protecting our loved ones from the specter of cyber threats that linger after we leave.” –
